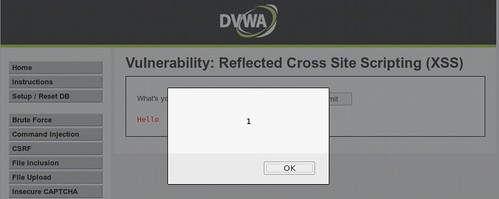
XSS in an input validation weakness which allows an attacker to inject a payload into a response from the application. When the payload can included HTML/Javascript commands this leads to command execution within the browser of the victim.
Reflected
The payload is executed within the immediate response to the request where it is injected.
Persistent
The payload is injected into a persistent datastore and then executes later in response to that payload being being retrieved from the datastore.
DVWA - Reflected Low
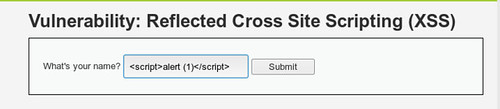
DVWA - Reflected Medium
Referring to source code, a str_replace function has be added to filter out the word < script>replacing it with a blank space. However, we can bypass this by using all capitals < SCRIPT> instead.

In these cases, it is often a good idea to also try a mixture or upper and closer case on the script tag, for example: sCrIpT or ScRiPt
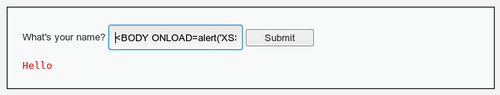
DVWA - Reflected High
Referring to the source code, a regular expression is being used to filter out the individual letters that make up the word script. Instead of using the work script we can try to use a bypass such as the img tag or a body tag: < BODY ONLOAD=alert('XSS')>